Hire Cloud Security Experts for your Business at Fair Cost
Schedule Free Consultation
Cloud security is a collection of policies, technologies, and controls that advance cloud data, applications, and infrastructure security. It ensures that sensitive data is not lost and, at the same time, enables businesses to work effectively in the cloud.
We provide cloud computing security services at Velan Remote IT Support to ensure the safety of your digital assets without compromising performance, accessibility, or compliance.
The primary goals of cloud security include:
Explore Our ServicesAt Velan Remote IT Support, we offer cloud security solutions for your business based on industry:
Industries differ in their cloud security needs based on data sensitivity, regulations, and operational risks. Velan Remote IT Support is an entity that provides tailored cloud security solutions so that organizations in regulated sectors can be stable, secure, and compliant.
We help healthcare organisations protect confidential patient information. Our security solutions are such that our medical records, clinical data, and digital health systems are secure and comply with HIPAA requirements.
With financial institutions, we deploy secure cloud environments that protect payment information. Our solutions will include secure payment processing systems, a fraud detection system, and compliance controls in line with PCI DSS standards.
We also help retail and e-commerce enterprises secure their online platforms. Our solution can avoid data breaches, secure transactions, and provide a secure shopping experience to customers.
We protect industrial systems, operational technology (OT), and cloud-connected IoT devices. We also keep supply chain information and production networks safe, so that no disruption or cyber threats affect operations.
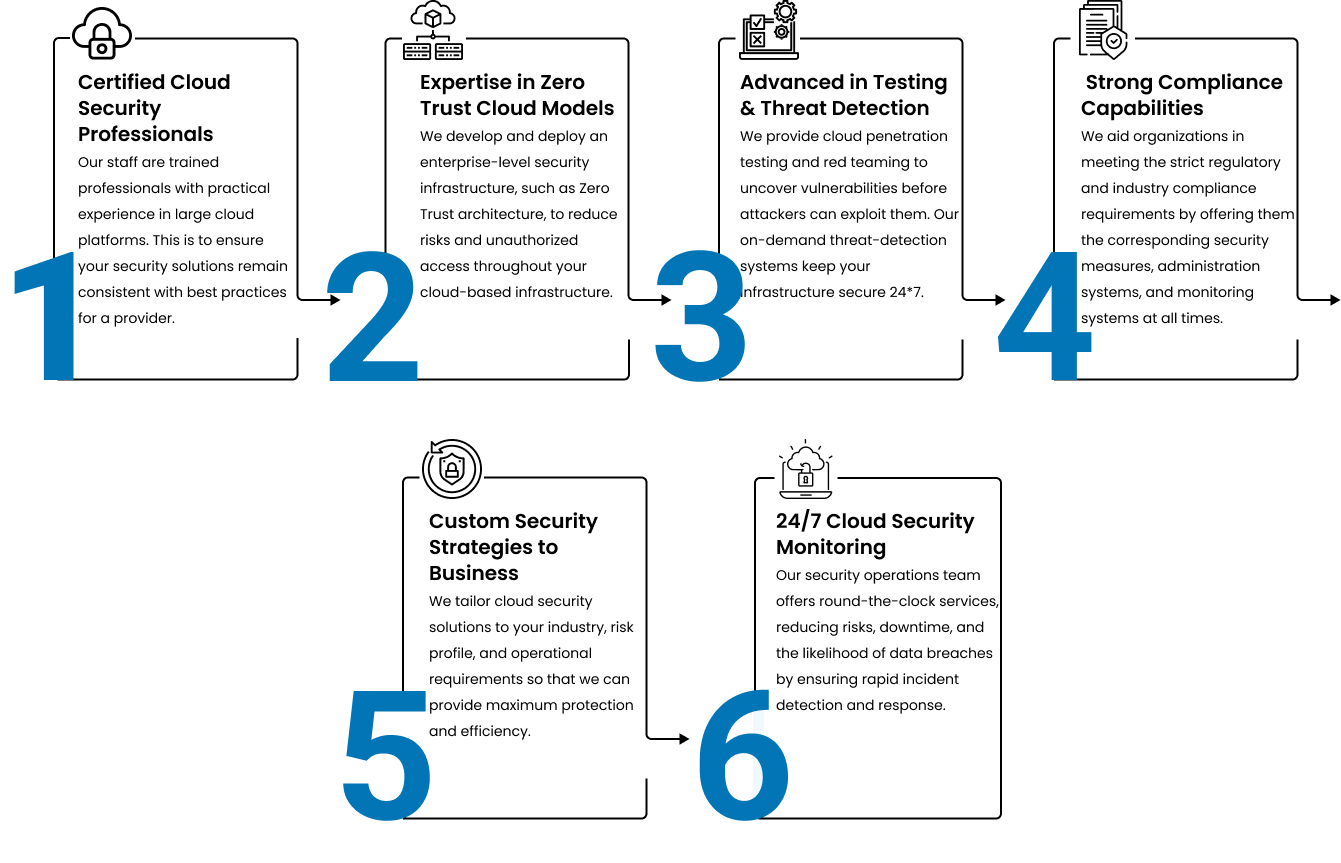
The six key pillars on which the overall cloud security strategy is based provide end-to-end coverage.
Allows access to cloud resources only to authorised users and systems through the use of strong authentication, role-based access, and identity monitoring.
Ensures the confidentiality of information by encrypting and classifying it, and uses data storage policies to prevent breaches and unauthorised access.
Emphasizes the application of firewalls, secure environments, a 24/7 firewall of cloud networks, servers, virtual machines, and storage.
Follows the best security practices all throughout the development, deployment, and maintenance of cloud-based applications, including regular testing and vulnerability assessments.
Monitors advanced security features and controls to detect, assess, and respond to cyber threats in real-time to decrease the risks that can be experienced.
Assures that cloud security policies are in compliance with regulatory and other compliance mandates, e.g., HIPAA, GDPR, and PCI, and are highly controlled, monitored, and reported.

We implement the full spectrum of cloud security services to cover all levels of your cloud infrastructure:
Tracks and controls access of employees and systems to the cloud applications to ensure secure use and avoid data leakage.
Profiles cloud configurations continuously to identify misconfigurations, security holes, and compliance failures before turning into risks.
Protects against cyber threats and vulnerabilities such as virtual machines, containers, and serverless functions.
Make sure your cloud platform complies with regulatory requirements such as HIPAA, GDPR, and PCI by constantly checking compliance.
Collects and processes security logs within your cloud infrastructure to detect and investigate threats and contribute to incident investigation.
Delivers highly unified endpoint, network, and cloud threat detection and response.
Provides cloud-based network security that integrates secure access and network connectivity in a unified platform.
Concentrates on enabling users to access cloud applications and data, ensuring safe, controlled consumption by organizations.
Cloud surroundings are open to emphasized security threats, which must be handled in advance.
At Velan Remote IT Support, we have the expertise, best practices, and positive mindset to defend your cloud environments with proactive security practices.
The key to a successful implementation of cloud security is an architecture comprising numerous layers of protection that work together to secure data, applications, and infrastructure.
IAM is used to manage cloud resources. Our authorized users are also protected by role-based access control, multi-factor authentication, and least-privilege access controls, which grant them an appropriate level of access.
DLP solutions can ensure that sensitive data does not leak, whether accidentally or intentionally. Through our services, the flows of information in the cloud are detected, sensitive information is identified, and security is implemented.
The other fundamental security measure is encryption, which ensures data security in transit and at rest. A strong encryption protocol is also used to protect all sensitive information, so unauthorised users will not be able to read it in the event of a breach.
SIEM systems offer real-time event monitoring and event analysis in the cloud. Logs of applications, networks, and infrastructures are collected and examined to identify suspicious activity, threats, and violations of compliance.
Using advanced AI tools and machine learning competencies, we persistently monitor, maintain, and regularize your servers.




Velan provides a full set of managed IT services for cloud, server, storage, and IT infrastructure. Explore our resources and get information on IT insights, emerging trends, and practical solutions.
Identify risks before they impact your business. Request your cloud security audit now.
Secure Your Cloud